Catalogue Search | MBRL
Search Results Heading
Explore the vast range of titles available.
MBRLSearchResults
-
DisciplineDiscipline
-
Is Peer ReviewedIs Peer Reviewed
-
Series TitleSeries Title
-
Reading LevelReading Level
-
YearFrom:-To:
-
More FiltersMore FiltersContent TypeItem TypeIs Full-Text AvailableSubjectCountry Of PublicationPublisherSourceTarget AudienceDonorLanguagePlace of PublicationContributorsLocation
Done
Filters
Reset
2,882
result(s) for
"Ciphers"
Sort by:
Can you crack the code? : a fascinating history of ciphers and cryptography
by
Schwartz, Ella, 1974- author
,
Williams, Lily, illustrator
in
Ciphers Juvenile literature.
,
Ciphers History Juvenile literature.
,
Cryptography Juvenile literature.
2019
\"Codes can carry big secrets! Throughout history, lots of good guys and lots of bad guys have used codes to keep their messages under wraps. This fun and flippable nonfiction features stories of hidden treasures, war-time maneuverings, and contemporary hacking as well as explaining the mechanics behind the codes in accessible and kid friendly forms. Sidebars call out activities that invite the reader to try their own hand at cracking and crafting their own secret messages. This is the launch of an exciting new series that invites readers into a STEM topic through compelling historical anecdotes, scientific backup, and DIY projects\"-- Provided by publisher.
Codes and ciphers: Julius Caesar, the Enigma and the Internet
by
Churchhouse, R. F
in
Ciphers
2009
The design of code and cipher systems has undergone major changes in modern times. Powerful personal computers have resulted in an explosion of e-banking, e-commerce and e-mail, and as a consequence the encryption of communications to ensure security has become a matter of public interest and importance. This book describes and analyses many cipher systems ranging from the earliest and elementary to the more recent and sophisticated, such as RSA and DES, as well as wartime machines such as the ENIGMA and Hagelin, and ciphers used by spies. Security issues and possible methods of attack are discussed and illustrated by examples. The design of many systems involves advanced mathematical concepts and this is explained in detail in a major appendix. This book will appeal to anyone interested in codes and ciphers as used by private individuals, spies, governments and industry throughout history.
Cryptography
by
Anderson, Rane, author
in
Cryptography Juvenile literature.
,
Ciphers Juvenile literature.
,
Cryptography.
2017
Cryptography is a powerful tool that been used throughout history. Learn to make and break the same ciphers used by monarchs, spies, and soldiers.
An Efficient Cryptosystem Using Playfair Cipher Together With Graph Labeling Techniques
2021
Cryptography is the branch of Discrete Mathematics which deals with the transmission of secret communications between intended parties without the knowledge of third party. Graph theory is the enchanting field if Mathematics that designate integers to edges and vertices through some established functions. In current scenario security of communication plays a crucial role in any telecommunication or network applications. In this paper we have proposed an efficient cryptosystem using play fair cipher together with graph labeling to safeguard our secret text from unauthorised persons. Here we employ the substitution cipher namely Play fair cipher for plaintext encryption and ourencrypted text in the form of Cipher Graph is forwarded to the receiver which on application of graph labeling yields our plaintext. Thus a fusion of the techniques Cryptography with Graph labeling provides ultimate security for secure transmission of data or information at various levels.
Journal Article
Lightweight Cryptography: A Solution to Secure IoT
by
Jindal, Poonam
,
Dhanda, Sumit Singh
,
Singh, Brahmjit
in
Algorithms
,
Communications Engineering
,
Computer Communication Networks
2020
In Internet of Things (IoT), the massive connectivity of devices and enormous data on the air have made information susceptible to different type of attacks. Cryptographic algorithms are used to provide confidentiality and maintain the integrity of the information. But small size, limited computational capability, limited memory, and power resources of the devices make it difficult to use the resource intensive traditional cryptographic algorithms for information security. In this scenario it becomes impertinent to develop lightweight security schemes for IoT. A thorough study on the lightweight cryptography as a solution to the security problem of resource-constrained devices in IoT has been presented in this work. This paper is a comprehensive attempt to provide an in-depth and state of the art survey of available lightweight cryptographic primitives till 2019. In this paper 21 lightweight block ciphers, 19 lightweight stream ciphers, 9 lightweight hash functions and 5 variants of elliptic curve cryptography (ECC) has been discussed i.e. in total 54 LWC primitives are compared in their respective classes. The comparison of the ciphers has been carried out in terms of chip area, energy and power, hardware and software efficiency, throughput, latency and figure of merit (FoM). Based on the findings it can be observed that AES and ECC are the most suitable for used lightweight cryptographic primitives. Several open research problems in the field of lightweight cryptography have also been identified.
Journal Article
Codebreaker : a novel
Seventeen-year-old Mia Hayes' world shatters when her mother is killed and her father disappears, leaving behind a coded message that sends her and a rebellious hacker on a high-stakes race through D.C. to uncover government secrets and stop a devastating attack.
A Sponge-Based Key Expansion Scheme for Modern Block Ciphers
2022
Many systems in use today require strong cryptographic primitives to ensure confidentiality and integrity of data. This is especially true for energy systems, such as smart grids, as their proper operation is crucial for the existence of a functioning society. Because of this, we observe new developments in the field of cryptography every year. Among the developed primitives, one of the most important and widely used are iterated block ciphers. From AES (Advanced Encryption Standard) to LEA (Lightweight Encryption Algorithm), these ciphers are omnipresent in our world. While security of the encryption process of these ciphers is often meticulously tested and verified, an important part of them is neglected—the key expansion. Many modern ciphers use key expansion algorithms which produce reversible sub-key sequences. This means that, if the attacker finds out a large-enough part of this sequence, he/she will be able to either calculate the rest of the sequence, or even the original key. This could completely compromise the cipher. This is especially concerning due to research done into side-channel attacks, which attempt to leak secret information from memory. In this paper, we propose a novel scheme which can be used to create key expansion algorithms for modern ciphers. We define two important properties that a sequence produced by such algorithm should have and ensure that our construction fulfills them, based on the research on hashing functions. In order to explain the scheme, we describe an example algorithm constructed this way, as well as a cipher called IJON which utilizes it. In addition to this, we provide results of statistical tests which show the unpredictability of the sub-key sequence produced this way. The tests were performed using a test suite standardized by NIST (National Institute for Standards and Technology). The methodology of our tests is also explained. Finally, the reference implementation of the IJON cipher is published, ready to be used in software. Based on the results of tests, we conclude that, while more research and more testing of the algorithm is advised, the proposed key expansion scheme provides a very good generation of unpredictable bits and could possibly be used in practice.
Journal Article
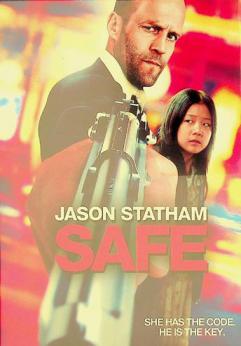
Safe
by
Yakin, Boaz film director
,
Bender, Lawrence film producer
,
Brunetti, Dana film producer
in
Gangsters Drama
,
Ciphers Drama
2011
When a second-rate cage fighter, Luke Wright, is tormented by the Russian Mafia and wanders the streets of New York, he witnesses a young Chinese girl, Mei, being pursued by the same mafia who want her for a priceless numerical code that they would kill for.
FPGA Modeling and Optimization of a SIMON Lightweight Block Cipher
2019
Security of sensitive data exchanged between devices is essential. Low-resource devices (LRDs), designed for constrained environments, are increasingly becoming ubiquitous. Lightweight block ciphers provide confidentiality for LRDs by balancing the required security with minimal resource overhead. SIMON is a lightweight block cipher targeted for hardware implementations. The objective of this research is to implement, optimize, and model SIMON cipher design for LRDs, with an emphasis on energy and power, which are critical metrics for LRDs. Various implementations use field-programmable gate array (FPGA) technology. Two types of design implementations are examined: scalar and pipelined. Results show that scalar implementations require 39% less resources and 45% less power consumption. The pipelined implementations demonstrate 12 times the throughput and consume 31% less energy. Moreover, the most energy-efficient and optimum design is a two-round pipelined implementation, which consumes 31% of the best scalar’s implementation energy. The scalar design that consumes the least energy is a four-round implementation. The scalar design that uses the least area and power is the one-round implementation. Balancing energy and area, the two-round pipelined implementation is optimal for a continuous stream of data. One-round and two-round scalar implementations are recommended for intermittent data applications.
Journal Article