Catalogue Search | MBRL
Search Results Heading
Explore the vast range of titles available.
MBRLSearchResults
-
DisciplineDiscipline
-
Is Peer ReviewedIs Peer Reviewed
-
Series TitleSeries Title
-
Reading LevelReading Level
-
YearFrom:-To:
-
More FiltersMore FiltersContent TypeItem TypeIs Full-Text AvailableSubjectCountry Of PublicationPublisherSourceTarget AudienceDonorLanguagePlace of PublicationContributorsLocation
Done
Filters
Reset
1,849,474
result(s) for
"SECURITY SERVICES"
Sort by:
Security beyond the state : private security in international politics
\"Across the globe, from mega-cities to isolated resource enclaves, the provision and governance of security takes place within assemblages that are de-territorialized in terms of actors, technologies, norms and discourses. They are embedded in a complex transnational architecture, defying conventional distinctions between public and private, global and local. Drawing on theories of globalization and late modernity, along with insights from criminology, political science and sociology, Security beyond the State maps the emergence of the global private security sector and develops a novel analytical framework for understanding these global security assemblages. Through in-depth examinations of four African countries - Kenya, Nigeria, Sierra Leone and South Africa - it demonstrates how global security assemblages effect the distribution of social power, the dynamics of state stability, and the operations of the international political economy, with significant implications for who gets secured and how in a global era\"--Provided by publisher.
The Sensation of Security
2023
The Sensation of Security
explores how private security guards are a permanent,
conspicuous fixture of everyday life in the Brazilian city of Rio
de Janeiro. Drawing on long-term ethnographic research
with security laborers, managers, company owners, and elite global
consultants, Erika Robb Larkins examines the provision of security
in Rio from the perspective of security personnel, providing an
analysis of the racialized logics that underpin the ongoing work of
securing the city. Larkins shows how guards communicate a
sensação de segurança (a sensation of security) to clients
and customers who have the capital to pay for it. Cultivated
through performances by security laborers, the sensation of
security is a set of culturally shaped racialized and gendered
impressions related to safety, order, well-being, and cleanliness.
While the sensação de segurança indexes an outward-facing
task of allaying fears of crime and maintaining order in elite
spaces, it also refers to the emotional labor and embodied worlds
that security workers navigate.
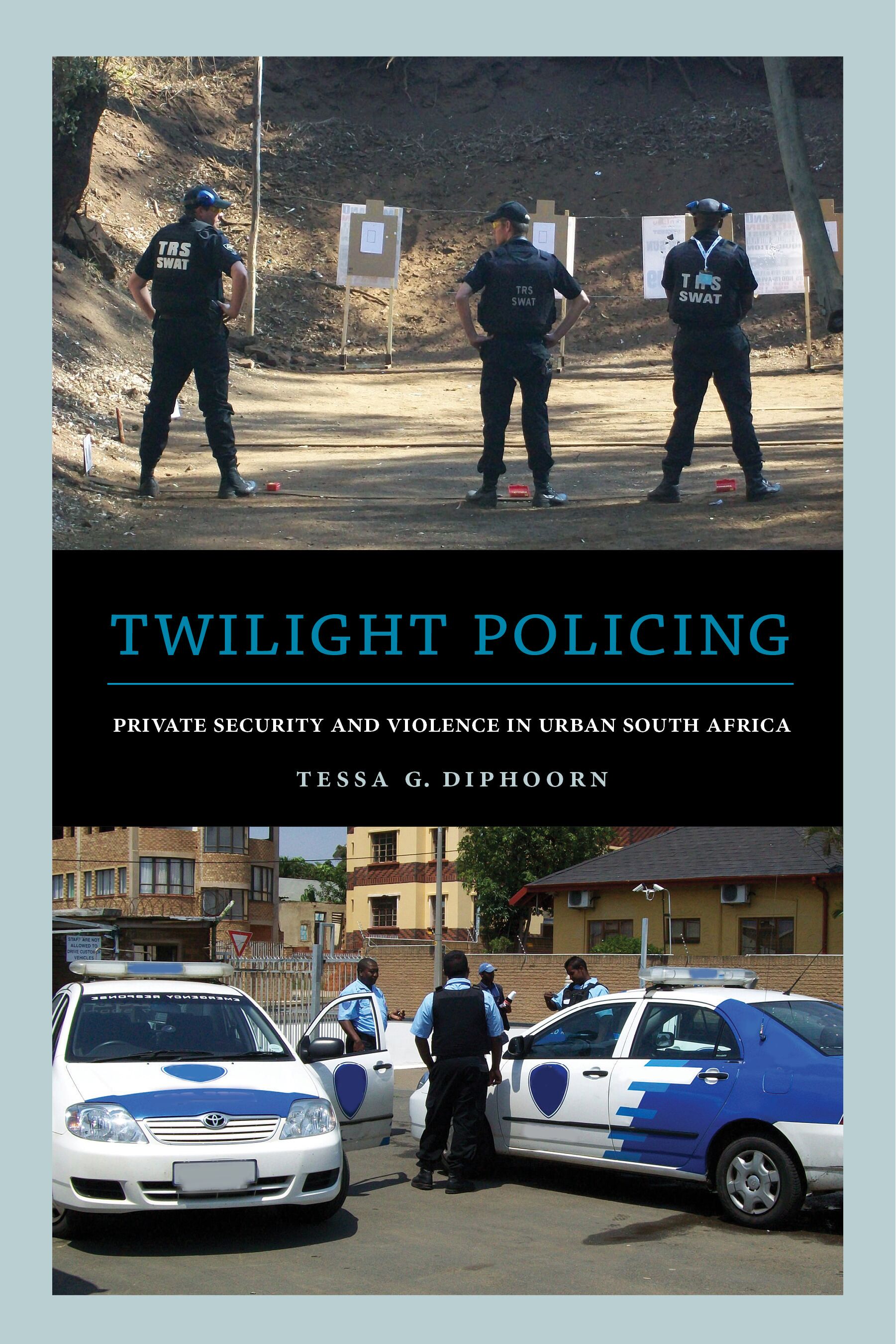
Twilight policing
2015,2016,2019
South Africa boasts the largest private security sector in the entire world, reflecting deep anxieties about violence, security, and governance. Twilight Policing is an ethnographic study of the daily policing practices of armed response officers—a specific type of private security officer—and their interactions with citizens and the state police in Durban, South Africa. This book shows how their policing practices simultaneously undermine and support the state, resulting in actions that are neither public nor private, but something in between, something \"twilight.\" Their performances of security are also punitive, disciplinary, and exclusionary, and they work to reinforce post-apartheid racial and economic inequalities. Ultimately, Twilight Policing helps to illuminate how citizens survive volatile conditions and to whom they assign the authority to guide them in the process.
Private security in Africa : from the global assemblage to the everyday
Across Africa, growing economic inequality, instability and urbanisation have led to the rapid spread of private security providers. While these 'PSPs' have already had a significant impact on African societies, their impact has so far received little in the way of comprehensive analysis. Drawing on a wide range of disciplinary approaches, and encompassing anthropology, sociology, and political science, this book offers unique insight into the lives and experiences of security providers and those affected by them, as well as into the fragile state context which has allowed them to thrive.
Outsourcing Information Security: Contracting Issues and Security Implications
by
Cezar, Asunur
,
Raghunathan, Srinivasan
,
Cavusoglu, Huseyin
in
Breaches
,
Complementarity
,
Contract incentives
2014
A unique challenge in information security outsourcing is that neither the outsourcing firm nor the managed security service provider (MSSP) perfectly observes the
outcome
, the occurrence of a security breach, of prevention effort. Detection of security breaches often requires specialized effort. The current practice is to outsource both prevention and detection to the same MSSP. Some security experts have advocated outsourcing prevention and detection to different MSSPs. We show that the former outsourcing contract leads to a significant disincentive to provide detection effort. The latter contract alleviates this problem but introduces misalignment of incentives between the firm and the MSSPs and eliminates the advantages offered by complementarity between prevention and detection functions, which may lead to a worse outcome than the current contract. We propose a new contract that is superior to these two on various dimensions.
This paper was accepted by Lorin Hitt, information systems.
Journal Article
Financial cybersecurity risk management : leadership perspectives and guidance for systems and institutions
Financial cybersecurity is a complex, systemic risk challenge that includes technological and operational elements. The interconnectedness of financial systems and markets creates dynamic, high-risk environments where organizational security is greatly impacted by the level of security effectiveness of partners, counterparties, and other external organizations. The result is a high-risk environment with a growing need for cooperation between enterprises that are otherwise direct competitors. There is a new normal of continuous attack pressures that produce enterprise threats that must be met with an array of countermeasures. This book explores a range of cybersecurity topics impacting financial enterprises, including the threat and vulnerability landscape confronting the financial sector, risk assessment practices and methodologies, and cybersecurity data analytics. Governance perspectives, including executive and board considerations, are analyzed as are the appropriate control measures and executive risk reporting.-- From publisher's description.
An Ontology-Based Cybersecurity Framework for the Internet of Things
by
Mozzaquatro, Bruno Augusti
,
Goncalves, Diogo
,
Agostinho, Carlos
in
Big Data
,
Cybersecurity
,
cybersecurity framework
2018
The use of sensors and actuators as a form of controlling cyber-physical systems in resource networks has been integrated and referred to as the Internet of Things (IoT). However, the connectivity of many stand-alone IoT systems through the Internet introduces numerous cybersecurity challenges as sensitive information is prone to be exposed to malicious users. This paper focuses on the improvement of IoT cybersecurity from an ontological analysis, proposing appropriate security services adapted to the threats. The authors propose an ontology-based cybersecurity framework using knowledge reasoning for IoT, composed of two approaches: (1) design time, which provides a dynamic method to build security services through the application of a model-driven methodology considering the existing enterprise processes; and (2) run time, which involves monitoring the IoT environment, classifying threats and vulnerabilities, and actuating in the environment ensuring the correct adaptation of the existing services. Two validation approaches demonstrate the feasibility of our concept. This entails an ontology assessment and a case study with an industrial implementation.
Journal Article
Private security in Africa
2017
“Across Africa, growing economic inequality, instability and urbanization have led to the rapid spread of private security providers. While these PSPs have already had a significant impact on African societies, their impact has so far received little in the way of comprehensive analysis. Drawing on a wide range of disciplinary approaches, and encompassing anthropology, sociology and political science, Private Security in Africa offers unique insight into the lives and experiences of security providers and those affected by them, as well as into the fragile state context which has allowed them to thrive. Featuring original empirical research and case studies ranging from private policing in South Africa to the recruitment of Sierra Leoneans for private security work in Iraq, the book considers the full implications of PSPs for security and the state, not only for Africa but for the world as a whole.”